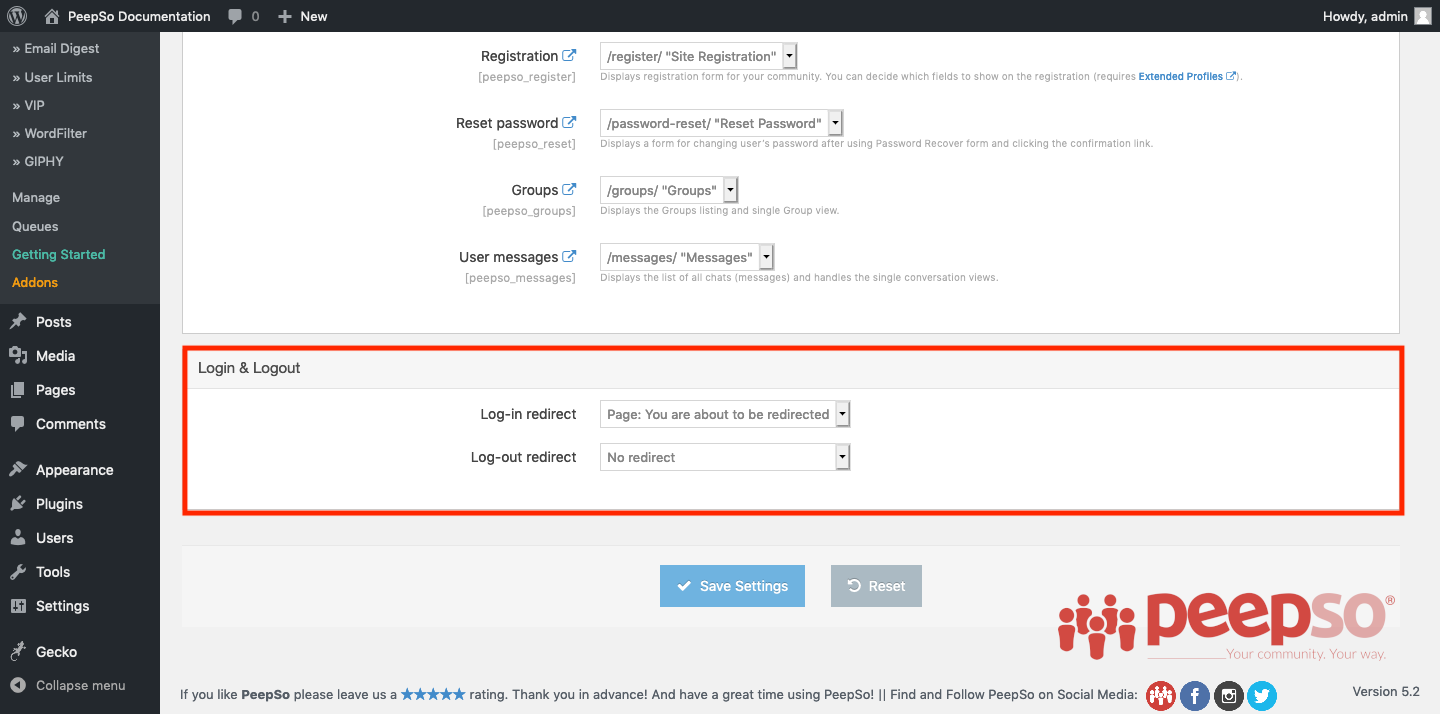
Redirection Options #
If you wish to redirect users after login or logout, you can do this in WP Admin -> PeepSo -> Configuration -> Navigation under “Login and Logout” panel.
#
Security #
Security settings can be found in WP Admin -> PeepSo -> Configuration -> Accounts and Security
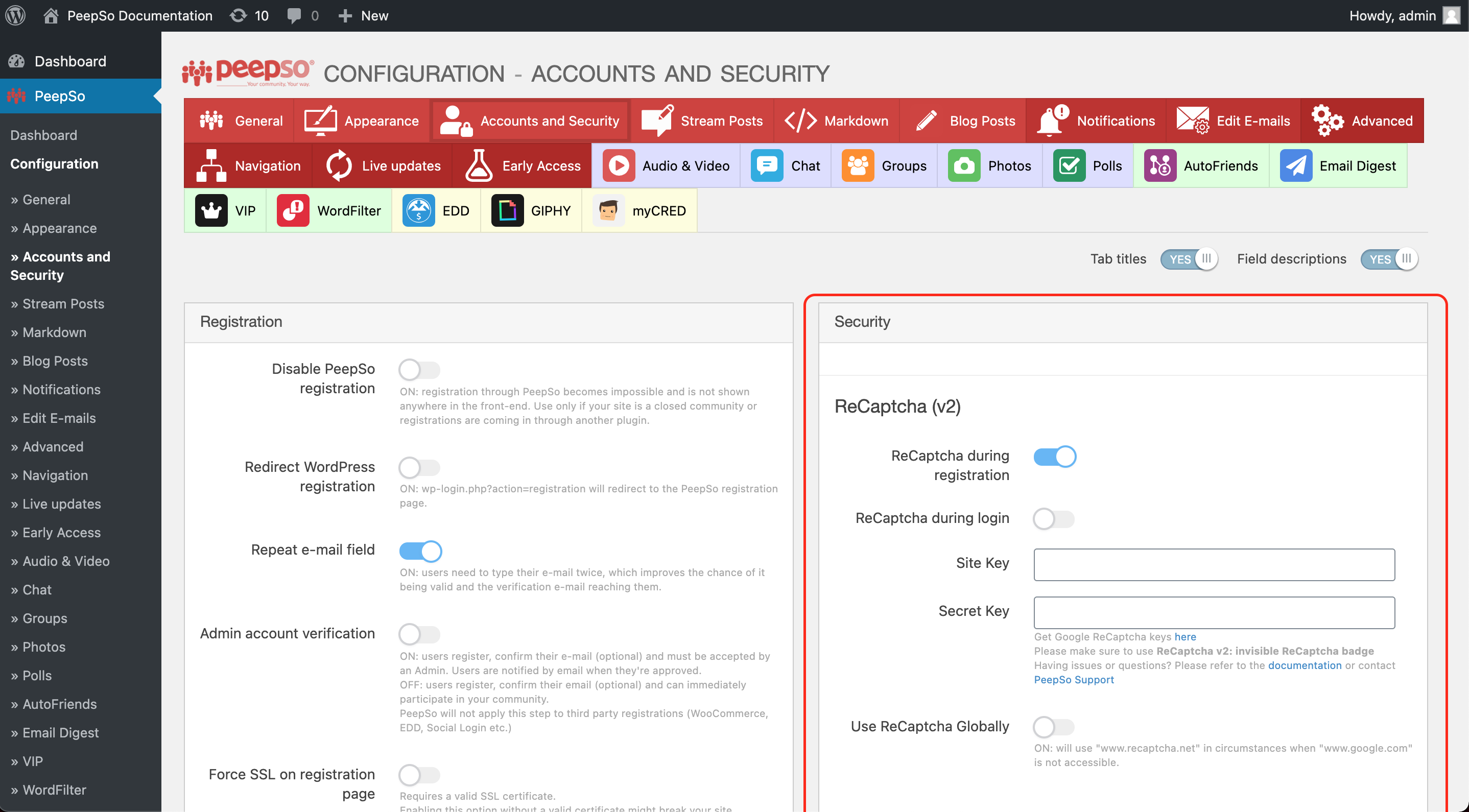
ReCaptcha #
- ReCaptcha during registration
Add invisible ReCaptcha to registration process - ReCaptcha during login
Add invisible ReCaptcha to login process - Site key
Google invisible ReCaptcha site key - Secret key
Google invisible ReCaptcha secret key - Use ReCaptcha Globally
Enable: will use “www.recaptcha.net” in circumstances when “www.google.com” is not accessible.
Password #
- Password strength requirements
Applies only to new passwords. You can set here how many characters in total are required. Also, the number of lowercase, uppercase, numbers, and special characters can be set here. - Password reset delay
since 2.8.0.0, admin can now define a custom delay between password reset requests (brute force protection).
#
Login Security #
- Check “remember me” by default
Enable: “Remember me” checkbox on the login form will be checked by default - Require e-mail to login
Since 3.2.0.0, Improves security by preventing username sign-in; email address is required to log in. Intended to apply to all login attempts: PeepSo, WordPress, and third party (if proper filters are implemented). “Administrators” are any users who have a manage_options cap and/or PeepSo Administrator role.- No – Use username/e-mail for login
- Administrators – Use e-mail login for Administrators only
- Everyone – Use e-mail login for everyone
- Enable Login brute force protection
Enable Login brute force protection settings - Block login after
Maximum failed attempts allowed. - Block for
hours: minutes – how long to block login attempts after the above limit is reached. - Email Notification
Send an e-mail notification to the user, warning them about failed login attempts. - Enable additional block after
Additional security when users block themselves repeatedly. - Additional block length
How long to block login attempts when additional security is triggered. - Reset retries after
How long it takes for the system to “forget” about a failed login attempt. - IP whitelist
list of IP addresses whitelisted from brute-force protection, one IP per line
#
Security & caching #
- Login nonce check
Disable security nonce check during PeepSo login. This will prevent PeepSo login failed error on highly cached systems, while using third-party caching plugins like WP Rocket, W3 Total Cache, Litespeed, or other similar plugins that return login failed error during the login, since PeepSo will stop validating the (potentially over-cached) security login nonce. Using this setting is generally not recommended, as it lowers the systems resilience against brute force attacks, but it will be reasonably safe in a properly configured and secure environment with brute force protection enabled. - Registration nonce check
Disable security nonce check during PeepSo registration. - Password reset nonce check
Disable security nonce check during PeepSo password reset. - Password preview
Enable: will display a button to toggle password preview in all PeepSo login forms and the registration form.
#
Note: All these settings will only work on PeepSo forms and PeepSo widgets. These settings will not take effect if you decide to use third-party login forms or widgets.