Blog
News & Tutorials
Create your perfect community. Just the way you always wanted to.
PeepSo and its plugins make it So Easy.
-
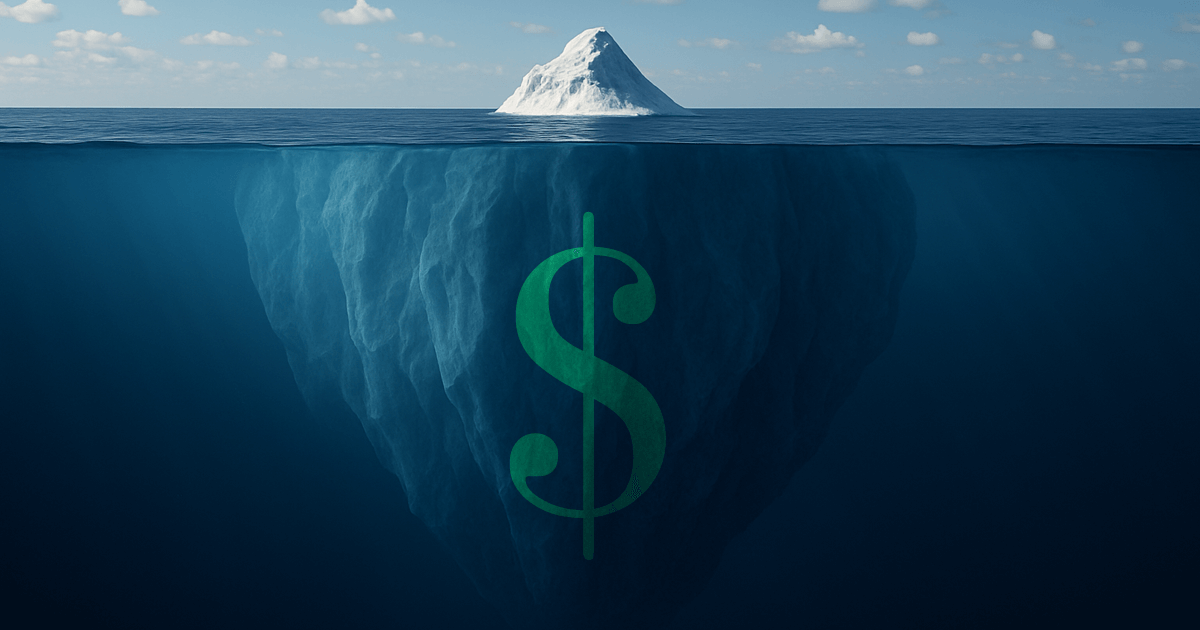
The Hidden Cost of Building Your Community on Facebook, X, or Reddit
For many creators, entrepreneurs, and organizations, building an online community is one of the most powerful ways to create real value. Communities bring people together around shared goals, passions, or identities. They generate conversations, inspire loyalty, and drive growth. But the question is: where should that community live?
Blog Categories
-
The Hidden Cost of Building Your Community on Facebook, X, or Reddit
For many creators, entrepreneurs, and organizations, building an online community is one of the most powerful ways to create real value. Communities bring people together around shared goals, passions, or identities. They generate conversations, inspire…
-

New Release: 7.0.5.0
We’re excited to announce the release of PeepSo 7.0.5.0, bringing you a range of usability improvements, smoother mobile experiences, and key fixes that make your community platform more polished and reliable than ever. From enhanced…
-

New Release: 7.0.4.4
This small release ships improvements to automatic updates, affected by the recent WordPress 6.8.
-

Important Security Release – 7.0.4.3
PeepSo 7.0.4.3 has just been released, and it includes a critical security update. If you’re using an earlier version, we strongly recommend updating immediately. This release addresses a vulnerability that, in rare and specific circumstances,…
-

PeepSo 7.0.4.1 Release – Smarter Search, Better UX, and Key Fixes
PeepSo 7.0.4.1 just dropped. It’s not flashy — it’s just solid.
-
Going Beyond a Simple Membership
For quite some time now, PeepSo and Paid Memberships Pro (PMP) work in a perfect harmony with the help of purposefully built integration plugin that is available in our PeepSo Ultimate Bundle. It gives you…
-
PeepSo 7.0.4.0 Is Live – Smarter, Safer, and More Seamless Than Ever
We’re thrilled to roll out PeepSo 7.0.4.0, a fresh update that brings smoother experiences, tighter security, and smarter customization to your community. Whether you’re an admin fine-tuning your platform or a member looking for better…
-

New Release: 7.0.3.0
We are thrilled to announce the release of PeepSo 7.0.3.0! This update brings exciting new features, improvements, and crucial fixes to enhance your community-building experience. Let’s dive into what’s new and improved!
-
Anonymous Posts and more
We are thrilled to announce the release of PeepSo version 7.0.2.0, packed with exciting new features, improvements, and fixes. Whether you’re building a thriving online community or fine-tuning your PeepSo-powered site, this update delivers tools…
All Posts
-

Important Security Release – 7.0.4.3
PeepSo 7.0.4.3 has just been released, and it includes a critical security update. If you’re using an earlier version, we strongly recommend updating immediately. This release addresses a vulnerability that, in rare and specific circumstances,…
-

PeepSo 7.0.4.1 Release – Smarter Search, Better UX, and Key Fixes
PeepSo 7.0.4.1 just dropped. It’s not flashy — it’s just solid.
-
Going Beyond a Simple Membership
For quite some time now, PeepSo and Paid Memberships Pro (PMP) work in a perfect harmony with the help of purposefully built integration plugin that is available in our PeepSo Ultimate Bundle. It gives you…
-
PeepSo 7.0.4.0 Is Live – Smarter, Safer, and More Seamless Than Ever
We’re thrilled to roll out PeepSo 7.0.4.0, a fresh update that brings smoother experiences, tighter security, and smarter customization to your community. Whether you’re an admin fine-tuning your platform or a member looking for better…
-

New Release: 7.0.3.0
We are thrilled to announce the release of PeepSo 7.0.3.0! This update brings exciting new features, improvements, and crucial fixes to enhance your community-building experience. Let’s dive into what’s new and improved!
-
Anonymous Posts and more
We are thrilled to announce the release of PeepSo version 7.0.2.0, packed with exciting new features, improvements, and fixes. Whether you’re building a thriving online community or fine-tuning your PeepSo-powered site, this update delivers tools…
Search
Get our latest eBook for free!
Treat this position as a necessary read for anyone who wishes to create a successful online community.
Stay in Touch
Sign up for our newsletter and be the first to know about news and latest releases.
Community by PeepSo
Super-light and free social networking plugin for WordPress