Following a full code audit and penetration test, this version delivers security and performance fixes that patch potential exploits with low-to-medium severity. It is strongly recommended to upgrade to PeepSo 2.3.0 as soon as possible. Gecko Theme 2.3.0.0 is also released alongside.
Security
About a week ago VDE Medical Software shared the results of a penetration test performed by Blue Frost Security for him. The report made us aware of a few small & medium issues and omissions that let the testers perform some unexpected actions in their testing environments. Although the bugs were not extremely severe and the replication of these bugs required pretty specific (and insecure) server setup in some cases, we took the matter very seriously.
File System
We fixed a potential path traversal exploit in Photos by completely removing the “download” feature and the related code. The AJAX endpoint used for the feature did not properly verify input, allowing a potential attacker to access files outside of the photos folder. Following this discovery we also performed a full internal audit of all parameters passed via GET and POST and used to manipulate the file system in any way and as a precaution added a tighter server-side MIME type checking for Audio & Video uploads.
Database
Following a discovery of a few potential SQL injection opportunities related to the sorting parameters, we implemented a new way to pass parameters that can only match a certain set of values (for example $sort can only be asc or desc). We also ran a full audit of all parameters passed to SQL queries: changed their type to int where applicable, forced a set of accepted data is possible and double checked nothing risky is happening otherwise.
Permissions
Three PeepSo AJAX endpoints had issues with permissions checks – either not performing them properly, or failing to halt the execution after detecting the lack of privileges. A potential attacker could do one of three things to someone else’s profile by exploiting the AJAX calls directly with good knowledge of how APIs work:
- change profile fields
- change preferences
- post on stream even if theoretically disabled
There was no exposure of critical profile information (e-mails, passwords etc.) as these are handled with different logic. Nothing could be changed without proper access rights, which is why this issue was labeled with medium severity.
Disabling Server Side Calls
The administrator is now able to disable link previews if he or she is worried that the users might exploit it to perform Server Side Request Forgery (SSRF). Essentially, when a link is embedded your server calls the target website to gather some information about it. A person with bad intentions can use your server as a proxy to execute scripts or look for exploits in another website by hiding behind your server calls. If you don’t have a high level of trust in your users or the legal situation forces you to have incredibly paranoid security standards, you should consider disabling embeds. If SSRF is worrying you, you should also not use Audio & Video, since embedding media also performs a server-side call and the aforementioned setting does not disable that.
E-mail Domain Whitelists And Blacklists
The UserLimits plugin now allows the administrator to define which e-mail domains are allowed (whitelist) or disallowed (blacklist), giving some rudimentary “first line of defense” filter for new registrations. Unrelated to security, the UserLimits plugin can now also limit the users’ ability to repost based on the same familiar old rules.
Other New Features And Improvements
PeepSo 2.3.0 was built on top of the unreleased code originally planned for 2.2.7, so some new features and improvements made it into 2.3.0 along with the major security effort.
Mentions (Formerly Tags) CSR
PeepSo 3.x will be a full REST API application, and to lighten the load on the process of migrating from 2.x., we gradually implement CSR (Client Side Rendering) in PeepSo 2.x whenever possible. In this version renamed the “Tags” feature to “Mentions” and moved the rendering engine from server-side (PHP) to Client Side Rendering (JavaScript). The same engine is now used to render author names on posts and comments. The user names and VIP icons are now rendered with strongly cached AJAX calls, which lessened the amount of repetitive SQL queries. The performance improvement is measurable – the server load in the case of our own website has visibly dropped.
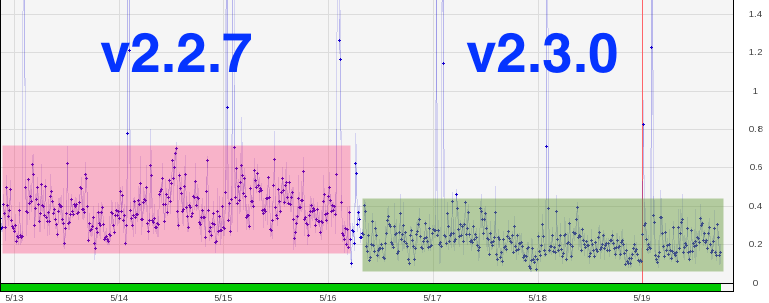
To put this into perspective. Average load on our own production server with PeepSo 2.2.7 was oscillating between 0.15 – 0.75. After we started using PeepSo 2.3.0 average load dropped to: 0.10 – 0.65. That’s about 15 – 30% improvement on average. If you’re not really a numbers person, just see the graph below.
Utilizing CSR To Build Human Readable Previews
As we move away from server-side parsing, it is increasingly difficult to build a human friendly post preview without all the Markdown, Mentions, etc. in it. Since our CSR engine has access to the final parsed content, it now passes the final result back to the server to store as a human readable cache (after stripping all HTML). Later we will be able to use these “humanized” previews in OpenGraph tags, notifications previews etc.
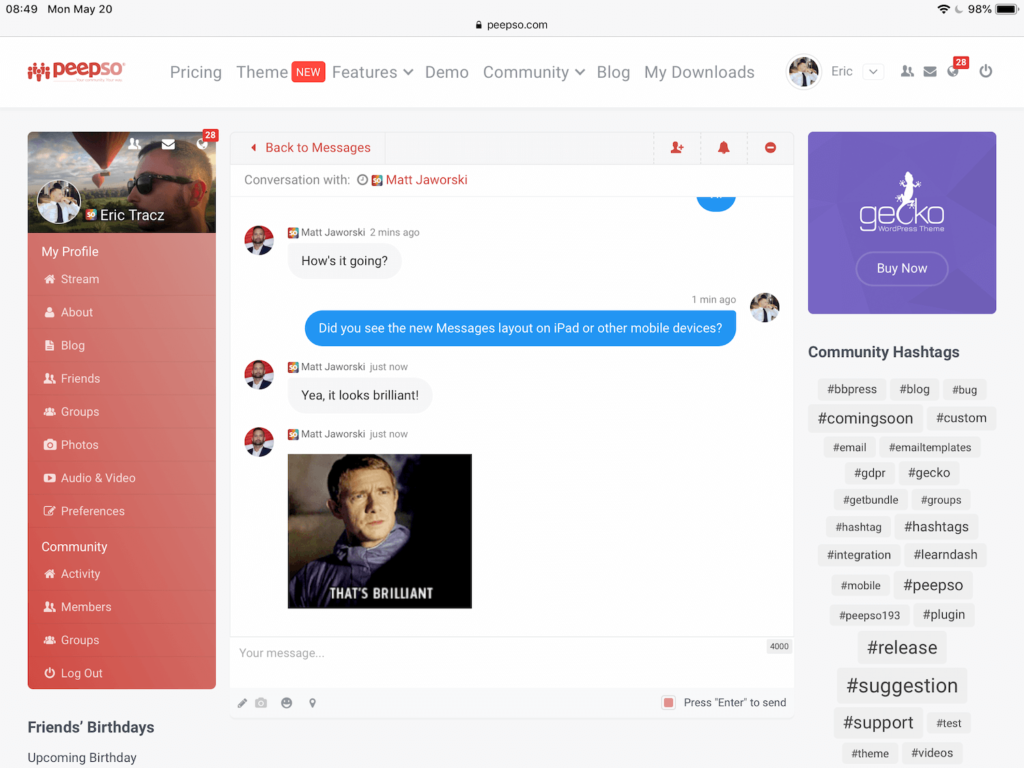
Messages UI Redesign
Messages view was something we wanted to change for a long time. We never had a chance to get it done, though. There was always something. Finally, we did manage to squeeze a UI update in this release. It works great not only on desktop view, but also on mobile devices like iPads.
Everything Else
We improved the Two Factor Authentication plugin detection to cover both free and premium versions, fixed PeepSo CSR (Client Side Rendering) interfering with blog titles containing the # character, improved searching of pinned group posts and a few minor visual
Gecko Theme 2.3.0.0
As usual, each PeepSo release is accompanied with a release of our Gecko theme. This release brings you new options per page that allow you to Hide header, Hide header menu & Hide footer. Again, that’s per page, so you’ll see those options in the right column, when editing a particular page. On the new options front, we also added a possibility to: hide header widget under icon on mobile view (Admin > Gecko > General tab).
We managed to also improve PeepSo group colors in Gecko Dark mode as well as fixed a wrong footer position on mobile devices. See the full changelog for both PeepSo and Gecko theme.
Special Thanks
Thank you again for sharing the results of the security audit with us, and helping us build a better and safer product for everyone.
Reactions & comments
Comments